I like it’s simplicity and ease of use. It could be a mini-password manager replacement with a couple of additions.
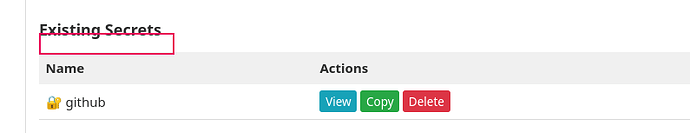
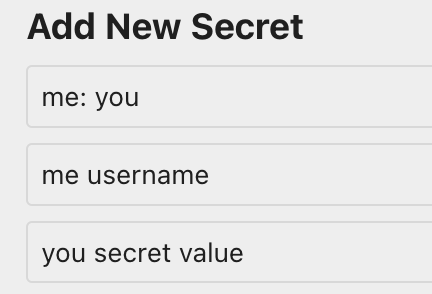
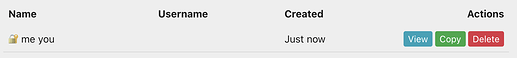
As the number of secrets grows, you need a filter to limit the secrets or to find a particular one. And it needs a copy button for the “secret” name because you often have to type that into a field as well. I guess having two fields per secret would actually be more normal, because for most services you need a username (which is kind of a secret) and the password.
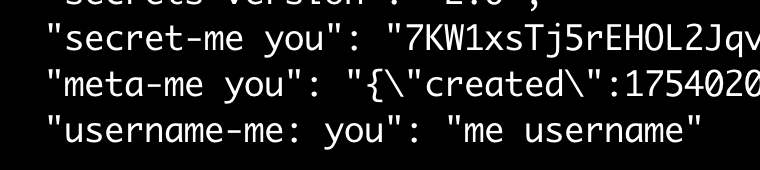
I often have situations where I want to share just a few passwords between systems, or where I’ve created a new password on one system that I will later enter into my standard password vault. Sometimes these passwords end up in insecure text files. But the real problem is that when I find them I don’t remember what they were for.  .
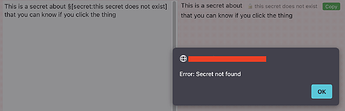
.
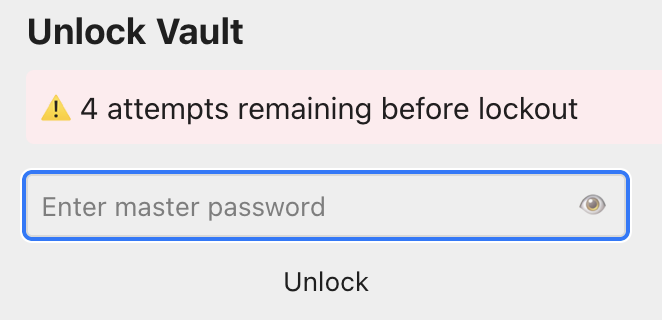
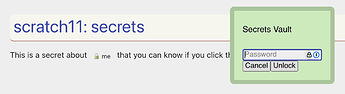
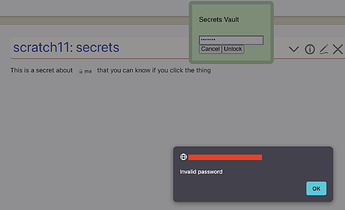
Some of the “features” of standard password managers make simple tasks so frustrating. Like a fast timeout that forces you to re-enter a pin, and then when you get back to the site you were setting up it’s timed out. And don’t get me started on the security “asterisks” that hide your password while you’re working from an android device where you have trouble typing even when you can see what you’re typing.
 ). In the future when this plugin matures, perhaps it could add a few custom importers/exporters for a GPG-compatible vault encrypted dump, a KeePass (which has a CLI-only mode) database or a
). In the future when this plugin matures, perhaps it could add a few custom importers/exporters for a GPG-compatible vault encrypted dump, a KeePass (which has a CLI-only mode) database or a